Locker Key Management Systems UK: Operational Control, Tracking and Access Governance
May 11, 2026
A locker key management system is not just a set of keys, locks or replacement parts. It is an operational framework used to issue, track, audit, replace and control locker access across a site. A strong system protects users, supports facilities teams, reduces lost key disruption and gives organisations a clear method for managing access over the full life of each locker.
This guide explains how locker key management systems work in schools, NHS settings, workplaces, industrial sites and leisure facilities. It covers key issuing, tracking, emergency access, duplicate control, master key hierarchy, audits, replacement workflows, RFID access, digital credentials and hybrid systems.
Use this page as the central operational guide for planning, improving or reviewing locker key control across a building, department or full estate.
Quick Answer: What Is a Locker Key Management System?
A locker key management system is a structured process for controlling who can open lockers, how access is issued, how keys are tracked, how losses are handled, how emergency access is managed and how locker access is audited over time.
| System layer | Purpose |
|---|---|
| Issuing | Controls who receives access and when. |
| Tracking | Records who holds each key, credential or access method. |
| Auditing | Checks that records, keys and locker access remain accurate. |
| Emergency access | Allows authorised staff to open lockers when needed. |
| Replacement | Restores access when keys are lost, damaged or unavailable. |
| Hierarchy | Defines master keys, department access and individual locker access. |
| Lifecycle management | Controls access from first issue through to return, rekeying or decommissioning. |
Why Locker Key Management Is an Operational System
Many organisations treat locker keys as small physical items. In practice, they are access-control assets. Each key, master key, RFID credential or digital permission decides who can open a storage point. That makes locker key management part of wider site governance.
A weak system creates recurring problems. Keys go missing. Staff waste time searching for spares. Lockers cannot be opened during urgent situations. Former users may still hold access. Duplicate keys may exist without authorisation. Audits become difficult because no one can prove who had access at a given time.
A strong system gives facilities, estates, school, healthcare and workplace teams a clear structure for issuing, recording, recovering and replacing locker access.
Core Locker Key Governance Principles
| Principle | What it means |
|---|---|
| Accountability | Every issued key or credential should be linked to a person, role, department or controlled location. |
| Continuity | Operations should continue when keys are lost, staff leave or emergency access is required. |
| Control | Only authorised people should be able to issue, duplicate, replace or override locker access. |
| Auditability | The organisation should be able to check access records, missing keys and replacement activity. |
| Scalability | The system should work for one locker bank, multiple departments or a full estate. |
| Lifecycle management | Access should be controlled from onboarding to return, reallocation or decommissioning. |
Operational Architecture of a Locker Key Management System
The operational architecture is the most important part of a locker key system. It defines how access is issued, tracked, audited, escalated and replaced. This is where locker key management moves beyond simple key supply and becomes a controlled facilities process.
1. Key Issuing
Key issuing is the point where locker access begins. The process should define who is allowed to receive a key, who approves the issue, how the issue is recorded and what happens when the user no longer needs access.
Issuing systems may be used for staff lockers, student lockers, visitor lockers, contractor lockers, temporary lockers, department lockers and shared-use facilities. The process can be paper-based, spreadsheet-based, software-based or connected to a wider access-control platform.
| Issuing requirement | Operational reason |
|---|---|
| User name or role | Shows who has responsibility for the locker. |
| Locker number | Connects the person to the physical storage point. |
| Key number or code | Supports replacement and tracking. |
| Date issued | Creates a clear access start point. |
| Authorising person | Shows who approved access. |
| Return date | Supports term-end, staff exit or temporary use control. |
For replacement ordering, see our guide to replacement locker keys cut to code.
2. Key Tracking and Accountability
Tracking records who currently holds each key or credential. This is essential for schools, NHS sites, offices, factories, gyms and any site with high user turnover.
A tracking system should identify issued keys, unissued keys, spare keys, master keys, lost keys, damaged keys and returned keys. Without this structure, facilities teams often depend on memory, informal handovers or incomplete records.
| Tracking field | Why it matters |
|---|---|
| Locker number | Identifies the physical locker. |
| Key code | Allows accurate replacement. |
| Holder | Shows who is responsible. |
| Status | Issued, returned, lost, damaged or spare. |
| Location | Useful for large sites and multi-building estates. |
| Notes | Records problems, rekeying or access restrictions. |
3. Escalation Procedures
Escalation procedures define what happens when locker access fails or becomes a security concern. This may include lost keys, suspected duplicate keys, broken locks, blocked access, unauthorised use or urgent opening requests.
Good escalation procedures prevent small access problems becoming wider operational disruption. They also protect staff from making informal access decisions without authorisation.
4. Locker Key Audits
Audits check whether locker access records match reality. They are especially useful at term end, staff exit, department moves, annual facilities reviews and before large replacement or retrofit projects.
A locker key audit should check issued keys, spare keys, missing keys, master keys, damaged locks, obsolete locks, user records and duplicate risks.
5. Duplicate Control
Duplicate control prevents uncontrolled key copying. This is important where lockers hold personal belongings, work equipment, medicines, PPE, uniforms, documents or valuable items.
Higher-security systems may use restricted keys, authorised duplication, approved order routes or controlled master key systems. For more secure estates, see master key locker systems.
6. Replacement Workflows
Replacement workflows allow an organisation to restore access when a key is lost, damaged or not returned. The workflow should identify the locker, confirm the key code, approve the replacement and update the tracking record after the replacement has been issued.
Where the lock type is unknown or the system is old, use a compatibility check before ordering. See our locker lock compatibility guide UK and locker lock replacement guide.
7. Emergency Access
Emergency access procedures define who can open a locker when normal access is unavailable. This may be needed for safeguarding, medical concerns, welfare checks, urgent maintenance, suspected misuse or operational emergencies.
The procedure should define who can authorise emergency opening, which access method is used, how the opening is recorded and how the locker is secured afterwards.
8. Key Hierarchy
Key hierarchy defines how individual keys, department keys, master keys and site-level access relate to each other. This is vital where one organisation manages multiple locker banks across several areas.
A simple site may only need individual locker keys and a controlled spare. A larger estate may need building-level, department-level and master-level access control.
Locker Key Lifecycle Diagram
The lifecycle of a locker key should be managed from the moment access is issued until the key is returned, replaced, archived or removed from service.
Locker Key Lifecycle
Master Key Hierarchy Diagram
Master key hierarchy should match the way the site is managed. This avoids giving too much access to the wrong people while still allowing authorised emergency and facilities access.
Example Master Key Hierarchy
- Site master: senior authorised access across the full estate.
- Building master: access for a specific building or block.
- Department master: access for a team, ward, floor or area.
- Locker bank access: access for a group of lockers.
- Individual locker key: user-level access to one locker.
Environment Layers: Locker Key Management by Setting
Different environments need different key management rules. A school does not manage locker access in the same way as a leisure centre, NHS site, factory or office. The system must reflect the users, risks, turnover and access requirements of the site.
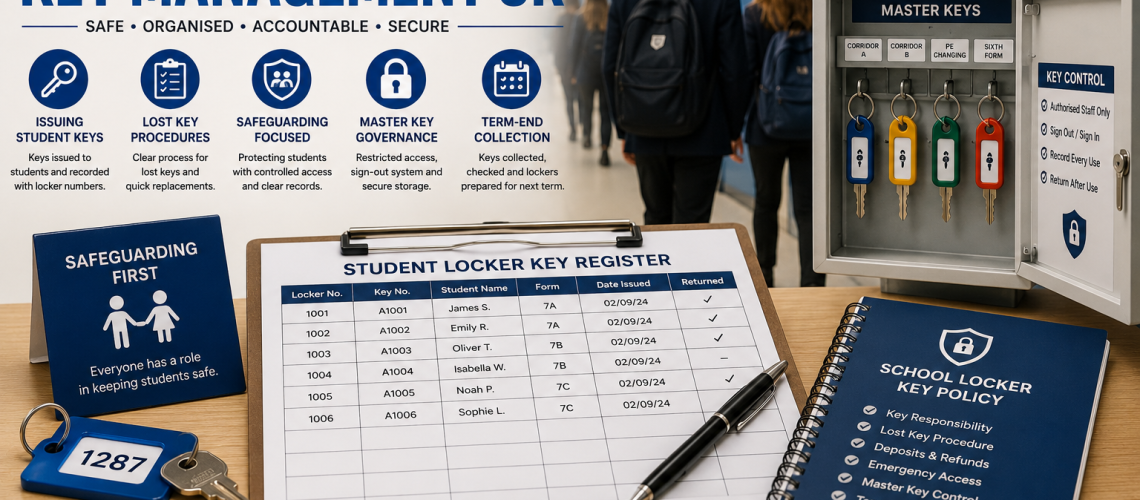
School Locker Key Management
Schools need clear systems for student allocation, safeguarding, term-end collection, lost key deposits, emergency access and corridor flow. Locker key records should support pastoral teams, reception staff, site managers and year-group administration.
Important school controls include student issue logs, parent or guardian communication, spare key control, master key governance and term-end recovery checks.
Related page: school locker key management UK.
NHS and Healthcare Locker Access Governance
NHS and healthcare settings need controlled staff access, clear audit records, emergency opening procedures and strong separation between personal storage, clinical storage and medicine-related areas.
Locker access should support authorised access, staff turnover, shift work, medicine-area security, emergency override and estates management.
Related page: NHS locker access and key governance UK.
Workplace Locker Access Control
Workplaces often manage permanent staff, hybrid workers, temporary staff, contractors and shared locker systems. The key management process should connect with HR, facilities management and staff onboarding or exit procedures.
Workplace systems should reduce lost key disruption, support shared-use lockers and make locker reassignment simple when staff roles change.
Related page: workplace locker access control systems UK.
Industrial and Warehouse Locker Key Management
Industrial sites often involve shift teams, PPE storage, contractor access, harsh environments and high-use locker areas. Key systems should be durable, easy to track and simple to replace when damage or loss occurs.
Where locker use is frequent or staff turnover is high, stronger tracking and replacement workflows are especially important.
Leisure and Public Facility Locker Access
Leisure centres, gyms, pools and public facilities often manage temporary users and shared-use lockers. Keyed systems, coin locks, combination locks, RFID systems and digital systems may all be suitable depending on the site.
Wet-area durability, reception control, user turnover and emergency opening procedures should be considered during system selection.
Environment Governance Matrix
| Environment | User turnover | Auditing need | Emergency access | Replacement frequency | Safeguarding | Operational complexity |
|---|---|---|---|---|---|---|
| Schools | High | High | High | Medium to high | Very high | High |
| NHS | Medium to high | Very high | Very high | Medium | High | Very high |
| Workplace | Medium | Medium | Medium | Medium | Low to medium | Medium |
| Leisure | Very high | Medium | High | High | Medium | High |
| Industrial | Medium to high | Medium to high | High | High | Low to medium | High |
Access Technology Layers
Locker key management can involve physical keys, master keys, RFID credentials, digital credentials or hybrid systems. The best option depends on user behaviour, site size, budget, audit needs and the level of operational control required.
Physical Keys
Physical keys remain common because they are simple, familiar and cost-effective. They work well for assigned lockers, staff lockers, student lockers and low-complexity environments.
The main challenge is tracking. A physical key system needs clear records, spare key control and a reliable replacement process.
Master Keys
Master keys allow authorised staff to open multiple lockers without holding every individual key. They are useful for facilities teams, school site managers, healthcare estates teams and emergency access procedures.
Master keys must be controlled carefully because they create wider access than individual keys.
RFID Locker Access
RFID locker systems use cards, fobs or wristbands to control access. They are common in leisure, workplace, education and smart storage environments.
RFID systems can reduce physical key loss and support faster allocation. More advanced systems may also support audit trails and temporary permissions.
Related page: RFID locker management systems UK.
Digital Credentials
Digital credentials may use apps, PINs, staff access systems or software-managed permissions. These systems are useful where organisations need scalable access control, flexible allocation or audit reporting.
Hybrid Locker Access Systems
Many sites do not move from keys to smart lockers in one step. Hybrid systems allow older keyed lockers, new RFID systems, digital credentials and manual override processes to operate during a phased upgrade.
Related page: hybrid locker access systems UK.
Access Technology Comparison Matrix
| System type | Auditability | Maintenance | Replacement complexity | Scalability | Security | Operational overhead |
|---|---|---|---|---|---|---|
| Keyed locks | Low to medium | Low | Low if key code is known | Medium | Medium | Medium |
| Combination locks | Low | Low to medium | Medium | Medium | Medium | Low to medium |
| RFID | Medium to high | Medium | Medium | High | High | Medium |
| Digital credentials | High | Medium to high | Low to medium | Very high | High | Medium to high |
| Hybrid systems | Medium to high | Medium | Medium | High | Medium to high | Medium |
Lifecycle Governance for Locker Key Systems
Lifecycle governance controls access from first issue through to return, loss, replacement, rekeying or decommissioning. This is especially important where lockers remain in service for many years but users change frequently.
Onboarding
During onboarding, the organisation should decide who needs a locker, which locker they receive, how access is issued and what records are created.
Assignment
Assignment connects a person, department or role to a specific locker. The record should include the locker number, key code, issue date and responsible person.
Return
Return procedures should be used when a student leaves, a staff member exits, a contractor finishes work or a temporary locker is no longer needed.
Loss
Lost key procedures should define reporting, replacement, possible charges, access restoration and whether the lock needs to be changed for security reasons.
Rekeying
Rekeying may be required after repeated losses, security concerns, department moves, stolen keys or major changes in user groups.
Decommissioning
When lockers are removed, replaced or upgraded, records should be closed and any remaining keys should be collected, destroyed or archived according to site policy.
Archive Logging
Archive logging keeps a record of previous access, old key codes, replacement history and lock changes. This helps future maintenance and supports long-term estate management.
Supporting Operational Pages
The pages below support this main locker key management systems hub. They provide deeper guidance for specific environments, security controls and access technologies.
Operational Control Pages
- School Locker Key Management UK — student issue, safeguarding, lost key deposits, term-end collection and emergency override.
- Workplace Locker Access Control Systems UK — hybrid workers, shared lockers, HR allocation and facilities control.
- NHS Locker Access and Key Governance UK — authorised access, staff-only areas, medicine-area support and emergency override.
- Restricted Key Systems for Lockers UK — restricted duplication, patented keyways and controlled security hierarchy.
- Locker Audit and Tracking Systems UK — audit logs, issue records, accountability and digital tracking.
Smart Access and Future System Pages
- Hybrid Locker Access Systems UK — mixed estates, phased migration and smart-plus-legacy locker systems.
- RFID Locker Management Systems UK — RFID credentials, software, audit logs and temporary permissions.
- Smart Locker Systems UK — software-led locker allocation, digital access and managed storage systems.
- Locker Electronic Locks UK — digital locks, electronic access and smart lock options.
Replacement, Maintenance and Compatibility Pages
- Replacement Locker Keys Cut to Code UK — ordering replacement keys by number or code.
- Locker Lock Compatibility Guide UK — checking whether replacement locks fit existing lockers.
- Locker Lock Replacement Guide UK — replacing worn, damaged or obsolete locker locks.
- Locker Lock Maintenance Guide UK — reducing failures through inspection and maintenance.
- Master Key Locker Systems UK — controlled override access and master key structures.
Downloadable Authority Assets to Produce
The following assets can turn this page into a stronger procurement, facilities and backlink resource.
| Asset | Purpose |
|---|---|
| Locker Key Audit Checklist PDF | Helps facilities teams check issued keys, duplicates, emergency access and returns. |
| Locker Key Policy Template UK | Provides a ready-made policy framework for schools, workplaces and estates teams. |
| Locker Key Issue Log Template | Supports day-to-day key allocation and return tracking. |
| Emergency Locker Access Procedure Template | Gives authorised staff a controlled process for urgent locker opening. |
Internal Link Engineering Plan
This page should become the central internal routing point for the locker key ecosystem. It should receive links from replacement, lock, school, workplace, NHS, smart locker and maintenance pages. It should also link back out to those pages using clear, descriptive anchor text.
Operational Links
- replacement locker keys cut to code
- locker lock compatibility guide UK
- locker lock maintenance guide
- master key locker systems
Environment Links
- school locker key management UK
- workplace locker access control systems UK
- NHS locker access and key governance UK
- industrial locker systems UK
- leisure locker systems UK
Technology Links
- smart locker systems UK
- RFID locker management systems UK
- electronic locker locks UK
- hybrid locker access systems UK
When Should an Organisation Review Its Locker Key System?
An organisation should review its locker key system when keys are frequently lost, users change often, emergency access is unclear, master keys are not controlled, lock types are mixed, records are incomplete or replacement ordering is difficult.
A review is also useful before changing lockers, upgrading locks, introducing RFID, moving departments, expanding a site or standardising storage across multiple buildings.
Final Summary
Locker key management is an operational control system. It covers issuing, tracking, auditing, emergency access, replacement, hierarchy, duplicate control and lifecycle governance. When managed properly, it reduces disruption, improves accountability and gives organisations a stronger framework for controlling locker access.
For sites with simple assigned lockers, a clear physical key issue log may be enough. For schools, NHS environments, workplaces, industrial sites and leisure facilities, stronger governance may be needed. This can include master keys, controlled replacement, restricted duplication, RFID, digital credentials or hybrid systems.
To plan the next step, start with the operational structure: who needs access, who controls access, how it is recorded, how it is audited and what happens when access fails.
Discover more from Blog Total Locker Service
Subscribe to get the latest posts sent to your email.