How to Manage Keys in the Workplace: Policies, Logs and Access Control
April 27, 2026
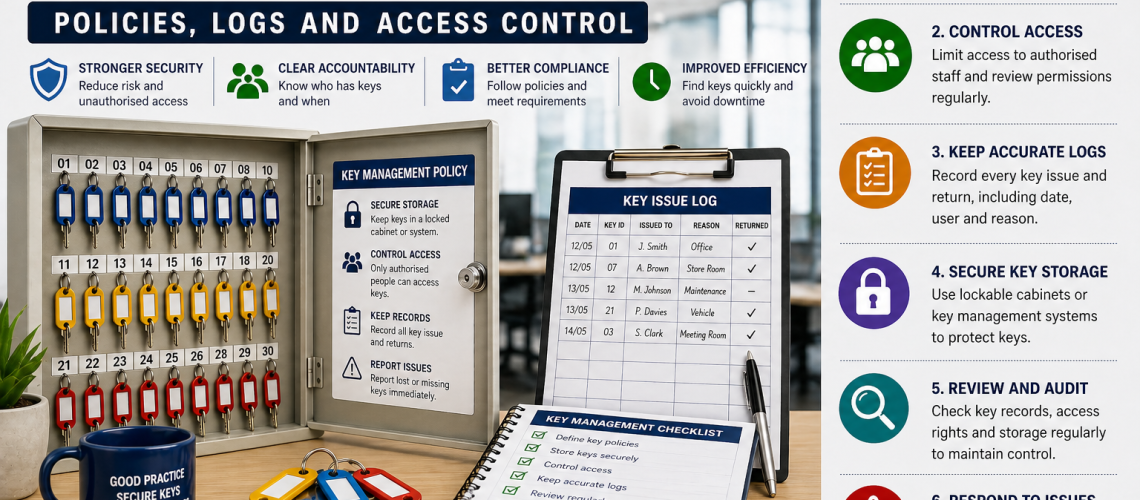
Workplace key management means controlling how keys are stored, issued, recorded, returned and reviewed. A clear system helps reduce lost keys, unauthorised access, security gaps and confusion between staff, managers and contractors.
Good key control is not only about buying a cabinet. It also depends on policy, access rules, staff responsibility, key logs and regular checks. Without those procedures, even a strong cabinet can be poorly managed.
This guide explains how to manage keys in the workplace using practical policies, key issue logs and access control procedures.
Why workplace key management matters
Keys often protect offices, stores, vehicles, plant rooms, lockers, cabinets, medicines, documents and restricted areas. When they are poorly controlled, the risk is not limited to one missing key.
A lost or misused key can lead to replacement locks, downtime, theft risk, unauthorised access and weak audit evidence. In regulated or security-sensitive environments, poor records can also create inspection and accountability problems.
Operational consequence: treat key control as a management process, not just a storage issue.
Create a workplace key management policy
A workplace key management policy sets out who can access keys, how they are issued and what staff must do when keys are returned, lost or damaged.
The policy should be short enough for staff to follow, but clear enough to remove doubt. It should also separate routine keys from higher-risk keys, such as master keys, vehicle keys and restricted-area keys.
- Who is responsible for key control
- Where keys must be stored
- Who can issue and receive keys
- Which keys need extra authorisation
- How key use must be recorded
- What happens when a key is lost
- How often key records are reviewed
A written policy also helps new staff, temporary workers and contractors understand the rules before they are given access.
Use a secure key storage system
Keys should not be left in drawers, open offices, unlocked cupboards or shared desk trays. A secure key storage system gives keys a fixed location and makes daily management easier.
Lower-risk workplaces often suit a lockable key cabinet with numbered hooks. Larger teams or environments with higher-risk keys may benefit from a digital key management system, which provides stronger control and clearer audit evidence.
For a wider comparison, see our guide to manual and digital key control systems.
Set access levels for different keys
Not every key needs the same level of control. A stationery cupboard key carries less risk than a master key, server room key, vehicle key or medicine cabinet key.
Start by grouping keys by risk. Then decide which staff roles can access each group. This keeps low-risk keys easy to manage while giving stronger protection to sensitive keys.
| Key type | Typical control level | Reason |
|---|---|---|
| General office keys | Standard cabinet access | Low risk and routine use |
| Store room keys | Named staff only | Protects stock and equipment |
| Vehicle keys | Logged issue and return | Supports accountability across users |
| Master keys | Senior approval or restricted access | High access risk |
| Restricted-area keys | Controlled access with review | Protects sensitive rooms or assets |
Takeaway: access level should follow risk, not convenience.
Keep a key issue log
A key issue log records when a key is removed, who has taken it and when it is returned. This can be a paper sheet, spreadsheet or electronic audit trail, depending on the system used.
The log should be simple. Staff are more likely to follow a process when it is quick and clear.
- Date and time issued
- Key number or description
- Name of person taking the key
- Reason for use, where needed
- Authorising person, where required
- Date and time returned
- Signature or digital confirmation
Paper logs can work well for small teams. Digital records are usually stronger where many users share keys or where evidence of use is important.
Label and identify keys clearly
Clear labelling prevents wasted time and reduces the risk of staff taking the wrong key. However, labels should not expose sensitive information if the key is lost.
Use numbered tags, colour coding or coded references rather than writing full door names or security-sensitive locations on every tag.
For example, “A12” is usually safer than “Main server room”. A separate controlled list can show what each code means.
Control master keys carefully
Master keys need stronger control because one key may open many doors, cabinets or restricted areas. Losing a master key can create a much wider security problem than losing a single low-risk key.
Access should be limited to named staff. Issue records should be complete, and managers should review master key use regularly.
Where the risk is high, consider storing master keys separately from routine keys or using a digital key control system with user-specific access records.
Manage contractor key access
Contractors may need temporary access to plant rooms, service areas, roof spaces, stores or maintenance cupboards. Their access should be controlled and time-limited.
Never rely on informal handovers. Record who received the key, why it was needed and when it was returned. For sensitive areas, a staff member may need to authorise or supervise access.
- Confirm contractor identity
- Issue only the keys needed for the task
- Record the time and purpose of access
- Set a return deadline
- Check keys back in before the contractor leaves site
Review key records regularly
Key control weakens when records are not checked. A regular review helps identify missing keys, outdated access rights and poor return habits before they become serious problems.
Small workplaces may only need a monthly check. Larger sites, multi-shift environments or higher-risk buildings may need weekly checks or automated reports.
The review should confirm that keys are present, labels are correct, access permissions remain suitable and any missing keys have been investigated.
What to do if a workplace key is lost
A lost key should be reported immediately. The response depends on what the key opens, whether it is identifiable and whether it could be used to access sensitive areas.
- Record the missing key
- Identify what the key opens
- Check the last known user
- Search likely locations
- Assess whether locks need changing
- Update the key register
- Review the process that allowed the loss
For low-risk keys, replacement may be simple. For master keys or restricted-area keys, lock replacement or rekeying may be necessary.
Key management checklist for workplaces
- Store keys in a secure cabinet or key control system
- Number hooks and tags clearly
- Use coded labels for sensitive keys
- Set access levels by key risk
- Keep a key issue and return log
- Restrict master keys to named staff
- Control contractor access
- Review records regularly
- Act quickly when keys are missing
- Update the policy when roles or buildings change
FAQs about workplace key management
What is workplace key management?
Workplace key management is the process of storing, issuing, tracking and reviewing keys used across a business or site.
Do workplaces need a key log?
A key log is strongly recommended where keys are shared between staff, contractors or departments. It helps show who used a key and whether it was returned.
Should master keys be stored separately?
Master keys should usually have tighter controls than routine keys. Depending on risk, they may be stored separately or restricted to named authorised users.
Is digital key control better than a paper log?
Digital key control is usually better for larger teams or higher-risk keys because it can provide stronger audit records. Paper logs can still work for small, lower-risk workplaces.
How often should key records be checked?
Key records should be checked regularly. Monthly checks may suit small sites, while larger or higher-risk workplaces may need weekly reviews or automated reporting.
Summary: how to manage keys in the workplace
Effective workplace key management combines secure storage, clear policies, controlled access, accurate logs and regular reviews. The aim is to make keys easy to manage without leaving gaps in security or accountability.
For small sites, a lockable key cabinet and simple issue log may be enough. For larger workplaces, shared access, contractor use or higher-risk keys, digital key control can provide stronger evidence and better operational control.
Discover more from Blog Total Locker Service
Subscribe to get the latest posts sent to your email.